
Categories
Evolving Cybersecurity Response: The “Respond” Function in CSF 2.0 Versus 2018
The capacity to respond effectively in a cybersecurity incident is critical for minimizing impact and restoring operations. The “Respond” function of the National Institute of
The Enhanced “Detect” Function in CSF 2.0: A Leap Forward from the 2018 Framework
In the evolving field of cybersecurity, the ability to quickly detect anomalies and cybersecurity events is crucial for maintaining the integrity of organizational assets. The
Fortifying Cybersecurity: Unpacking the Enhancements in CSF 2.0’s ‘Protect’ Function
The need for robust cybersecurity measures has never been more apparent in the rapidly advancing digital landscape. With cyber threats becoming increasingly sophisticated, the National

SecurityGate Unveils New Channel Program
HOUSTON, April 16, 2024 /PRNewswire/– SecurityGate, the provider of the leading SaaS platform for OT cyber improvement, is excited to announce the launch of its new
Deep Dive into the “Identify” Function: Transitioning from the 2018 Framework to CSF 2.0
Understanding an organization’s digital assets and systems in the ever-changing cybersecurity landscape is crucial to ensure effective security. The “Identify” function of the National Institute

Announcing General Availability of ISA/IEC 62443-2-1 Workflow in the SecurityGate Platform
We are thrilled to share that we have added ISA/IEC 62443-2-1 to the SecurityGate Platform. This update will assist users in creating a robust IACS
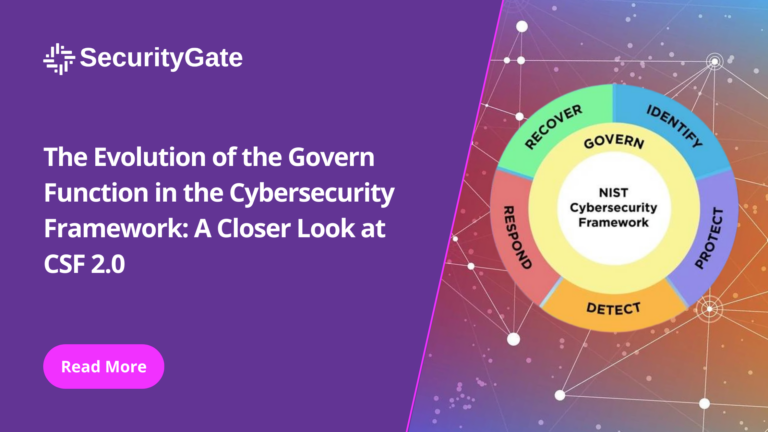
The Evolution of the Govern Function in the Cybersecurity Framework: A Closer Look at CSF 2.0
In the realm of cybersecurity, staying ahead of threats necessitates not just reactive measures but a proactive and structured approach to safeguarding digital assets. The
Fortifying the Frontlines: Navigating the Complexities of Application Layer Security
Welcome to another engaging session at Tea with C, where we unravel the mysteries of cybersecurity one layer at a time. Today, our focus ascends

Unveiling the Interpreter: Fortifying the Presentation Layer’s Role in Cybersecurity
Welcome back to Tea with C. As we navigate deeper into the OSI model, today’s spotlight shines on Layer 6: the Presentation Layer. The Presentation

Unpacking CSF 2.0: Navigating the Cybersecurity Landscape
In the fast-evolving world of cybersecurity, staying ahead of threats requires constant vigilance and a robust framework for managing risk. The National Institute of Standards

Navigating the Depths of Cybersecurity: Mastering the Session Layer for Enhanced Protection
In the constantly changing domain of digital security, it is essential for cybersecurity professionals to have a deep understanding of fundamental concepts. Today, I am

SecurityGate Implements NIS2 Directive Article 21.2 Cybersecurity Risk Management Measures into Platform
We are thrilled to announce the release of the NIS2 Directive Article 21.2 onto our platform. This will help our European customer base comply with
Mastering the Digital Currents: The Crucial Security Role of the Transport Layer
As we continue our journey through the OSI model, today’s focus shifts to Layer 4: the Transport Layer. This layer holds a special place in

Securing the Digital Frontier: The Vital Role of the Network Layer in Cybersecurity
Welcome back to our cybersecurity exploration, Tea with C series. Today, we delve into the heart of network architecture and its guardian role in cybersecurity:

Top Three Reasons Standardizing Your Assessment Workflows Accelerates Your Cyber Journey
In an era where cybersecurity threats gain sophistication by the day, critical sector organizations are under increasing pressure to defend against these threats and do